The largest single attack against Ukraine by Russian Shahed-136 type drones last week led to an unusual discovery. Technicians from a Ukrainian drone training and development company said they found a 4G modem with a SIM card from the Ukrainian Kyivstar telecom firm inside some of the downed drones. This could have implications of varying degrees of impact.
The Victory Drone company initially suggested on Telegram that the SIM card and modem could be used by Russia to track the remains of down drones, gain additional navigation via cell phones or telemetry “to adjust the flight mission in real-time.”
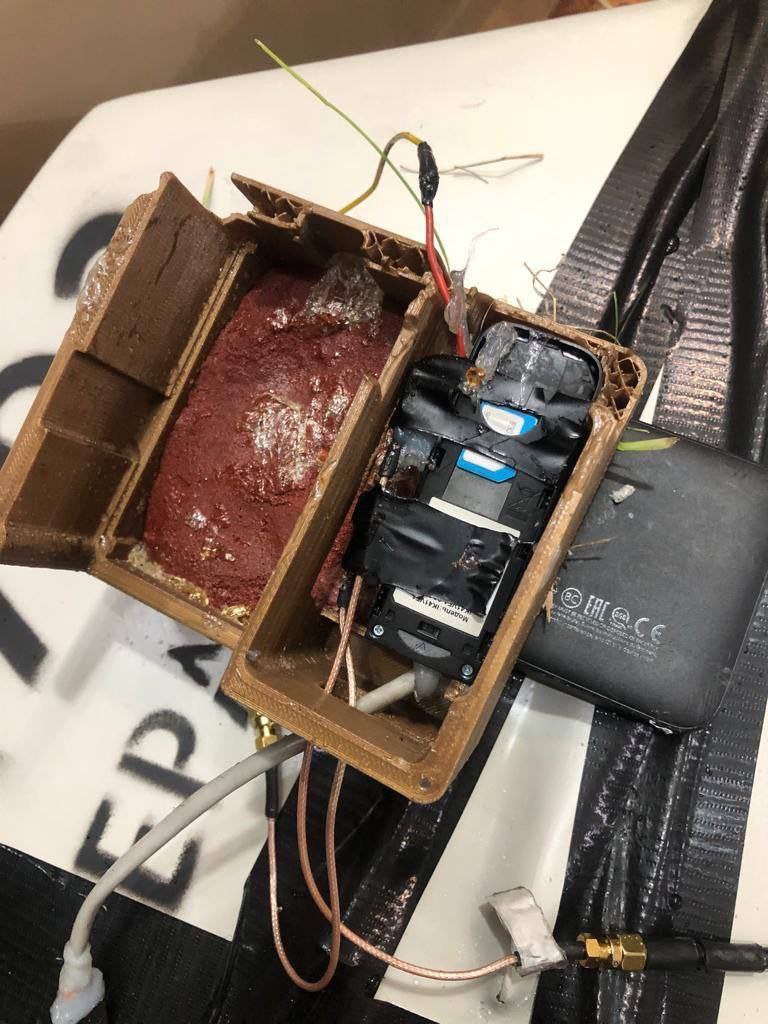
A subsequent post added more detail about what they found.
“On the night of the extreme mass attack of the Shahed, we intercepted a strong signal from the air as the Shahed flew through observation points,” Victory Drone said. “Several downed bombs were equipped with [Long Term Evolution] LTE mobile modems with [multi-input, multi-output] MIMO antennas. Everything was mounted on tape.”
From observing the drones’ seemingly jury-rigged innards, the Victory Drone technicians concluded “we are dealing with Russian Federation experiments, and not a serial product.”
As to why Shahed-136s would be equipped with cellular communications, there are a number of possibilities. Doing this to track drones after they crash, assuming they remain intact at all and this modification is not noticed, seems unlikely, although it’s possible. Using cell towers to help navigate may be possible, but that would require integration with the drone’s autopilot among other modifications. Still, even updating the drone’s position intermittently using network-provided geolocation could help correct for GPS disruption and error. This is especially relevant as Russia is trying to overcome GPS-denial tactics.
But using cellular networks to enhance drone capabilities is not a new idea, it’s something we have discussed for years. Drones can leverage cellular data in lieu or in addition to traditional datalinks. In urban environments, where cellular coverage is very robust, this can be highly beneficial as the dense urban environment means line-of-sight datalinks are severely limited in range, especially when operating very near or even inside structures. A drone that requires constant man-in-the-loop control can get that via the commercially available bandwidth phone companies provide anywhere in a city. This greatly expands the flexibility of drone operations in these environments. Obviously, there are also emerging security risks when it comes to how nefarious actors could potentially leverage this off-the-shelf capability.

But there are other applications, as well. Just taking advantage of cellular connectivity opportunistically throughout a drone’s flight, especially long-range ones like Shahed-136s execute, can allow for burst updates to be sent back to their launch units telling their position and status. This connectivity would be highly intermittent, but that is not an issue.
Using this very basic concept of operations, units can track the drone’s movement over time, even if sporadically, to ensure they make it to or very near their target. If they stop responding, it can be assumed they were shot down. This can provide near real-time intelligence as to which routes are proven to be safe, even if temporarily, and which are not, for follow-up attacks. In addition, if a drone makes it to its intended target while connecting to cellular networks, it can be assumed it likely hit its target, thus providing immediate mission success information.

Albeit imperfect, Russia’s limited reconnaissance capabilities, especially far forward into denied territory, means rapid bomb-damage/mission success assessments for its drones and missiles are a major challenge. By having a good indication a Shahed-136 made it to its target means follow-up attacks are not needed.
Actually changing the Shahed-136’s route in real time via cellular connectivity could be possible, but only in very simple terms. There is no man-in-the-loop and beyond-line-of-sight communications with the drones, so simply commanding it on a different pre-programmed route mid-flight based on actionable intelligence could be useful, but this is a more complex affair.
There are other possibilities, like this setup being paired with a basic onboard electronic surveillance system. This way the drone can send back signatures of air defense systems it detects and their azimuths via a cellular network. This would be simple data, but if multiple drones over an area are providing it, those emissions could potentially be triangulated to give away the location of air defense radars, for instance. Once again, this is less likely and there has been no talk of such a system being installed onboard the drone, but it is certainly not an exotic application. In fact, Shahed variants and similar drones they are loosely based on exist for homing in on these active emissions and destroying the emitter.
Regardless of the goal, there is a major drawback to this functionality though. These drones give off little electromagnetic radiation as they fly pre-programmed routes and have no active sensors. This is one of their greatest advantages. When you put a cellular communications system on them, they emit a telltale signature, one that is omnidirectional and moving through the air at relatively high-speed (compared to say cars on the ground). Electronic surveillance measures (ESM) can detect and even geolocate these emissions, giving away the drone’s presence and even its general position. This can allow for air defenses to more easily be brought to bear on the intruder.

Photo by YASUYOSHI CHIBA/AFP via Getty Images
The most common way to detect lower-end drones today is via this type of passive electronic surveillance, not radar, for instance, although usually these systems are looking for the frequencies used by two-way datalinks. Still, its a major vulnerability.
While this modification is certainly interesting, it isn’t surprising for reasons stated above and because we have seen the rapid evolution of the Shahed-136 since their initial use well over a year ago. This has included new warhead designs and changes to the type’s manufacturing processes, as well as new countermeasure paint, and more. With major dollars flowing to Iran to build and improve the drones, and Russia now working to produce them itself, we are seeing far more complex derivatives appear, including jet powered models with multiple seekers, which you can read all about here.
So, whether this is just an experiment or something greater, it is just another battlefield innovation and evolution of the Shahed-136 system. And it certainly will not be the last we will see.
Author’s note: modified the navigation section to include cellular positioning updating as a solid possibility.
Contact the author: Tyler@thedrive.com and Howard@thewarzone.com
